Mounting regulatory pressure and heightened customer expectations are prompting firms to turn to KYB tools in pursuit of seamless onboarding and robust AML compliance. However, the multi-phased nature of KYB has, in some cases, encouraged a piecemeal approach to process improvement, with institutions leveraging point solutions to augment different aspects of the workflow. Whilst this represents a marked improvement from manual, spreadsheet-based analysis, a fragmented technology stack can inadvertently act as a roadblock to true automation.
Although effective in isolation, if the products do not integrate with and complement one another, using different conceptual frameworks, calculations or data sources and formats, their combination may fail to achieve adequate risk oversight. Further, the ongoing work required to connect these systems is a distraction from truly automated processing. By adopting a more holistic perspective, and a comprehensive platform, firms can significantly improve the efficiency and effectiveness of their KYB process, facilitating smoother onboarding and better compliance outcomes.
A day in the life: Analysts with fragmented KYB
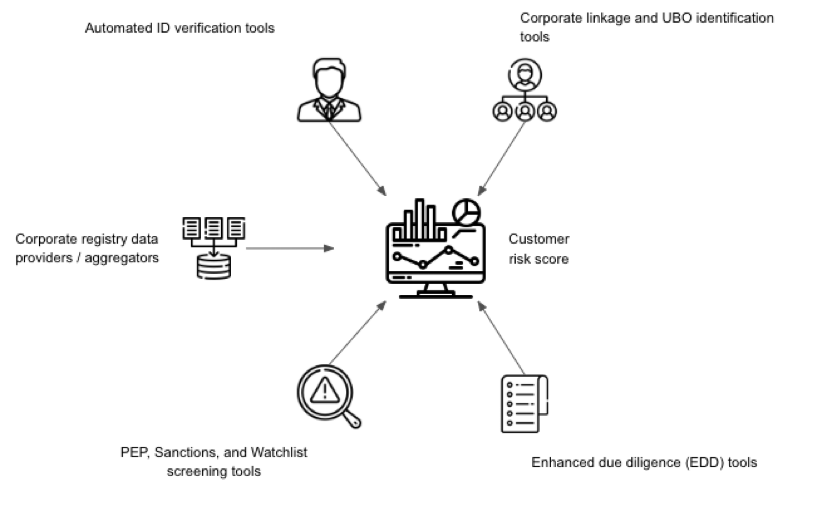
At the commencement of the onboarding process, analysts are tasked with gathering and verifying the basic business information, the company name, registration number, address and more. Due to the inherent challenges associated with accessing data, such as the varied approaches taken across corporate registries, analysts will often turn to specific corporate registry data providers to methodically validate this data.
Once the analyst has confirmed the existence of the onboarding organisation, the business information will be input into an automated UBO discovery solution, designed to unravel corporate structures to map and visualise complex ownership hierarchies.
This allows the analyst to pinpoint those individuals who hold significant control over the entity, noting their identities and ownership percentages. These individuals must then be processed using an identity verification software to capture and validate identification documents and biometric data.
By this point, the analyst has leveraged their suite of tools to discern the legitimacy of the business, determine its beneficial owners and prove the authenticity of their identities. From here, both the business and those with significant control need to be passed through PEP, sanctions and watchlist screening tools to check them against various high-risk lists. The analyst carefully reviews any matches to determine if further action is required.
For businesses and individuals flagged as potentially high-risk, the analyst turns to enhanced due diligence (EDD) software to conduct more in-depth investigations into the client’s financial background, operational activities, and potential connections to illegal practices.
Finally, the outputs from each of the aforementioned solutions must be aggregated in order to form a complete risk assessment. The decision maker must assign a risk score to the client based on the findings from each tool, potentially using yet another tool, making a go or no-go onboarding decision, ensuring all documentation and justifications are meticulously recorded.
Challenges
Data fragmentation
Different vendors often operate unique systems and databases, inadvertently creating silos where crucial information is stored in disparate locations. This segregation limits the firm’s ability to obtain a holistic view of customer and business relationships, leading to delays and inefficiencies as teams must manually extract, transfer, and input data across systems to complete the due diligence process.
This reconciliation is further complicated in cases where vendors provide data in varying formats and structures. For instance, pulling KYB data from an API while collecting individual identity assessments through batch processing may lead to errors and inconsistencies, making it difficult for compliance teams to align data across platforms.
Visibility and control limitations
Besides the operational burden associated with manually rekeying data into different systems, firms may also be exposing themselves to unnecessary financial, regulatory and reputational risk. When data is dispersed across multiple systems, customer risk scoring and real-time monitoring becomes challenging. Compliance professionals may struggle to promptly identify, document and address certain customer risks as data aggregation processes can introduce latency and errors.
Increased operational complexity
The coordination required to manage multiple vendor engagements should not be underestimated. Compliance personnel and senior management may need to liaise with each vendor, both during implementation and on an ongoing basis, to ensure the assessment mechanisms and outputs are akin to their ever-evolving risk appetite.
This coordination is often complicated further by differing service level agreements, data and software update frequencies and customer support protocols. Additionally, integrating multiple vendor systems with internal compliance platforms can often demand significant IT resources and expertise.
Hidden costs
Vendor pricing models and associated discounts may be based on onboarding volumes or user numbers. Without a unified platform, institutions may not be able to leverage aggregated volumes to negotiate a lower per-action or per-user cost. This issue is potentially exacerbated by overlapping functionalities which may cause some firms to pay for redundant services and/or features, driving up the total cost of ownership without necessarily providing additional value.
Audit trails
Regulators demand detailed documentation pertaining to onboarding and risk scoring to verify that firms have systematically followed the mandated due diligence processes. Such documentation establishes accountability by providing a clear audit trail, demonstrating that decisions are based on consistent, documented procedures rather than arbitrary judgments.
Achieving clarity is difficult when each stage of the KYB process involves different systems and tools that generate distinct outputs. The manual aggregation process can lead to inconsistencies, potential errors, and incomplete documentation, increasing the risk of gaps during compliance reviews.
The unified approach to KYB
Replacing your existing systems can seem daunting, but it’s not entirely necessary with a solution like NorthRow. Our KYB solution serves to streamline your existing processes by seamlessly integrating with your current technology stack, enhancing data cohesion and operational efficiency.
The platform itself offers real-time verification for companies and individuals, ensuring compliance and improving the customer experience. By aggregating data into a unified view without requiring a complete overhaul, NorthRow simplifies onboarding, improves accuracy, and reduces complexity. Its configurable system enables precise information collection and dynamic risk scoring, minimising false positives and enhancing compliance and risk management throughout the customer journey.
It is the end-to-end solution that you may have been trying to build and maintain yourself, done for you. It’s the choice to take your KYB to the next level, without the burden. Why wait? Get in touch today.







